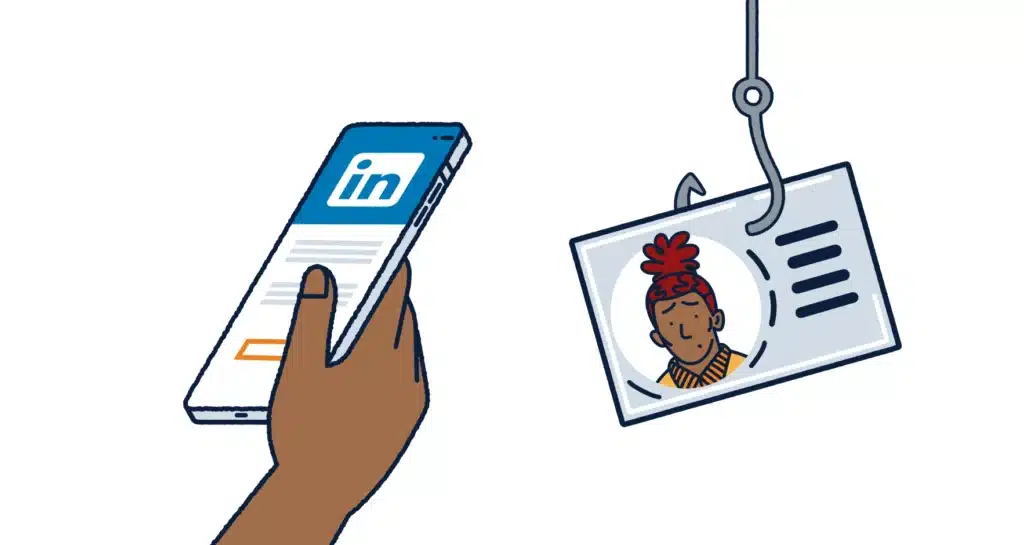
In the high-stakes world of cryptocurrency, the promise of a lucrative job opportunity can blur your instincts faster than you expect. I learned that the hard way. What looked like a serious offer from a crypto firm in Abu Dhabi turned into a meticulously engineered trap designed to exploit trust, ambition, and technical confidence. Many job seekers are now falling victim to the dangerous LinkedIn Crypto Job Scam. This is my first-hand account of the osascript Webex crypto job scam that almost compromised my Mac.
In fact, my experience is a perfect example of a LinkedIn Crypto Job Scam. It is not just a cautionary story. It is a detailed breakdown of how a modern, multi-layered attack unfolds in real time. From the initial LinkedIn exchange to the critical moment a malicious script was almost executed on my machine, I will unpack exactly how this scam operated, the red flags I nearly ignored, and the immediate recovery steps I took. If you use macOS, work in crypto, or value your digital assets, this is the journey you need to read.
The Anatomy of the osascript Webex Crypto Job Scam: A First-Hand Account
The osascript Webex scam is not amateur phishing. It is structured, patient, and technically aware. It preys on professional credibility and mirrors legitimate recruitment processes with unsettling precision. My experience unfolded in clear stages. Each stage lowered my guard just enough to make the next one feel reasonable. The attackers built trust through relevant technical questions, thoughtful back-and-forth emails, and a professional rhythm that matched genuine hiring processes. Nothing felt rushed. Nothing felt sloppy. That is what made it dangerous.
The Lure: A Legitimate-Looking Crypto Opportunity on LinkedIn
Like many genuine roles in our industry, it started on LinkedIn. I had applied for a crypto-related position and sent my CV through the platform as normal. The responses came back quickly, but not suspiciously quickly. The recruiter asked detailed questions about token launches, wallet integrations, and previous blockchain projects. The technical depth felt real. The cadence felt real. The company profile looked legitimate.
I remember thinking, “This is a serious opportunity.”
The conversation stretched over days. We exchanged emails. I answered follow-up questions. The tone remained professional throughout. There were no broken sentences or obvious red flags. If anything, the process felt more thorough than many real interviews I have had. That thoroughness was the hook. It built credibility. It lowered my defences.
The Setup: A Convincing Webex Link and Malicious DMG Download
After the initial email, I was invited to a Webex interview. The link looked authentic. The page resembled the official Cisco Webex interface down to the smallest detail. There were no obvious misspellings in the domain. The branding looked correct.
I was instructed to download a specific .dmg file. As a Mac user, downloading DMG files is routine. I have done it hundreds of times. The file mounted like any other macOS disk image. Nothing screamed danger.
That familiarity worked in their favour. It felt procedural. It felt technical. It felt normal.
The Trap: The Terminal Instruction That Felt Wrong (and Why it’s Dangerous)
The moment everything shifted came after opening the DMG. Instead of a standard graphical installer, I saw an application bundle that displayed a simple instruction: drag and drop this file into Terminal to begin.
That sentence stopped me.
Legitimate meeting software does not require manual Terminal execution. Professional assessment tools do not bypass standard macOS installers. My instinct pushed back immediately. But I hesitated. The pressure of the “interview” context nudged me forward. I did not want to appear technically incapable or resistant.
Dragging a file into Terminal exposes its path. Executing it can trigger hidden shell commands or osascript instructions. This bypasses standard macOS security prompts for unsigned apps and allows direct system-level execution. In simple terms, I would be handing over execution privileges to an unknown script.
The Revelation: Permission Requests That Exposed the Threat
After executing the instruction, macOS reacted instantly. Permission prompts appeared one after another.
Access to Notes.
Access to Desktop.
Access to Downloads.
That cascade of permission requests snapped everything into focus. No interview tool needs immediate access to personal folders. No legitimate recruiter requires system-wide data visibility.
In that moment, the illusion collapsed.
I denied every request. I shut the session down. I disconnected from the network. The pressure vanished and clarity returned. This was not an interview. This was an attempted system compromise.

Understanding the Threat: What osascript Enables and Why Crypto Professionals Are Targets
To understand the seriousness of this attack, you need to understand osascript. It is a legitimate macOS command-line utility that executes AppleScript and JavaScript for Automation. It can control applications, access files, and automate system behaviour. That power makes it valuable for developers. It also makes it dangerous in the wrong hands.
A malicious osascript command can access Desktop files, read browser data, trigger further downloads, or establish persistence. Because osascript is built into macOS, it does not look like foreign malware. It blends into the system. If a user grants permissions, the script operates with trusted access.
The Psychological Play: How Ambition Reduces Scrutiny
The technical layer matters. But the psychological layer is what nearly caught me.
The attackers invested time. They mirrored legitimate hiring processes. They asked relevant questions. They behaved professionally. That patience built emotional investment. I wanted the opportunity to be real. That desire softened my scrutiny.
Ambition narrows focus. When you believe you are progressing toward something meaningful, you justify unusual steps. You rationalise discomfort. That is how social engineering works. It does not force you. It guides you.
Why Crypto Professionals Face Elevated Risk
Crypto professionals sit in a high-value category. We manage wallets, private keys, exchange credentials, and project data. A single successful compromise can unlock significant digital assets. Unlike traditional banking systems, crypto transactions often offer no reversal mechanism.
That financial asymmetry motivates attackers. They will spend days building credibility if the potential reward justifies it. When I realised the target profile, the logic became obvious. I was not randomly selected. I was strategically approached.

Immediate Incident Response: What to Do If You’ve Executed a Suspicious Script
The moment you suspect compromise, act immediately. Disconnect from Wi-Fi. Unplug Ethernet. Deny all permission prompts. Force quit suspicious processes.
I moved straight into audit mode. I opened Activity Monitor. I checked running processes. I scanned for rogue osascript instances using Terminal commands. I reviewed active network connections. I inspected LaunchAgents and LaunchDaemons directories for unfamiliar persistence files.
I examined shell profile files for injected commands. I searched for recently created hidden files. I cross-referenced timestamps around the execution moment. I treated my machine like a forensic environment.
Post-Audit: Securing Your Digital Life
After confirming no active persistence, I rotated critical passwords. Apple ID. Email. Exchanges. Everything. I reviewed 2FA settings and trusted devices. I monitored login activity logs.
Even if no compromise appears visible, assume risk. Move assets if necessary. Consider hardware security keys. Evaluate wallet integrity. If doubt remains, perform a clean macOS reinstall from a pre-incident backup.
Proactive Defence: Safeguarding Your Mac and Digital Assets from Advanced Threats
Looking back, the red flags stand out clearly. Terminal-based installation. Subtle domain variations. The emotional momentum of opportunity.
My new protocol is simple. I independently verify every company. I manually type official domains. I cross-reference recruiter identities. I slow down during permission prompts. I never execute unfamiliar files through Terminal.
Discomfort is a signal. When something feels wrong, pause. Investigate. Ask questions. A legitimate employer will not pressure you into bypassing standard security practices.

The Final Hurdle
The osascript Webex crypto job scam exposed how sophisticated modern cyber threats have become. This was not crude phishing. It was layered, patient, and psychologically aware. It weaponised trust and technical familiarity.
The lesson is clear. Technical knowledge alone does not guarantee safety. Vigilance, scepticism, and disciplined incident response do. Treat your Mac and digital assets as high-value targets, because they are.
Do not let ambition override caution. Share this experience with colleagues in crypto and beyond. Audit your systems. Strengthen your defences. Stay alert.
Disclaimer: This account reflects a personal experience combined with established cybersecurity practices. It is intended for educational purposes. Readers facing active compromise should consult qualified cybersecurity professionals for advanced incident response guidance.


