RenEngine Loader is not merely a piece of malware; it’s a stealthy, multi-stage delivery system meticulously engineered to evade detection and deliver information-stealing payloads. This malware threat is particularly dangerous because its primary function is to establish a foothold on a victim’s machine and subsequently download and execute more dangerous secondary malware.
Kaspersky Threat Research initially identified samples of RenEngine Loader as early as March 2025, demonstrating Kaspersky’s proactive threat intelligence and continuous protection of users from this evolving threat since its discovery [1]. According to Pavel Sinenko, Lead Malware Analyst at Kaspersky Threat Research, “RenEngine Loader represents a concerning trend in malware sophistication. Its multi-stage approach, combined with clever evasion tactics, makes it a significant challenge for users without robust security solutions” [2]. This section delves into the intricate workings of RenEngine, revealing how it operates and why it poses such a significant risk.
The Infection Chain Unravelled: From Launch to Payload Delivery
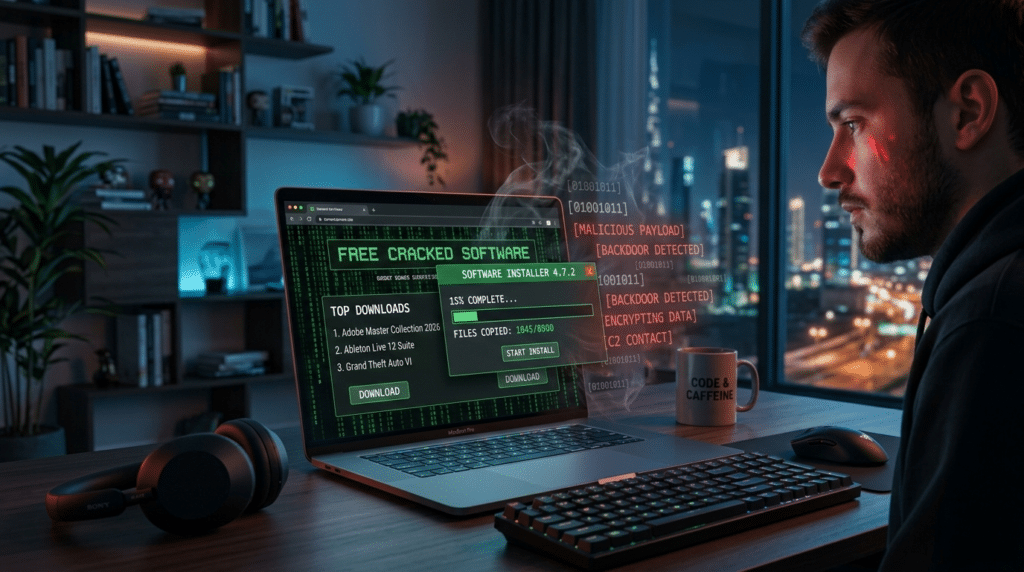
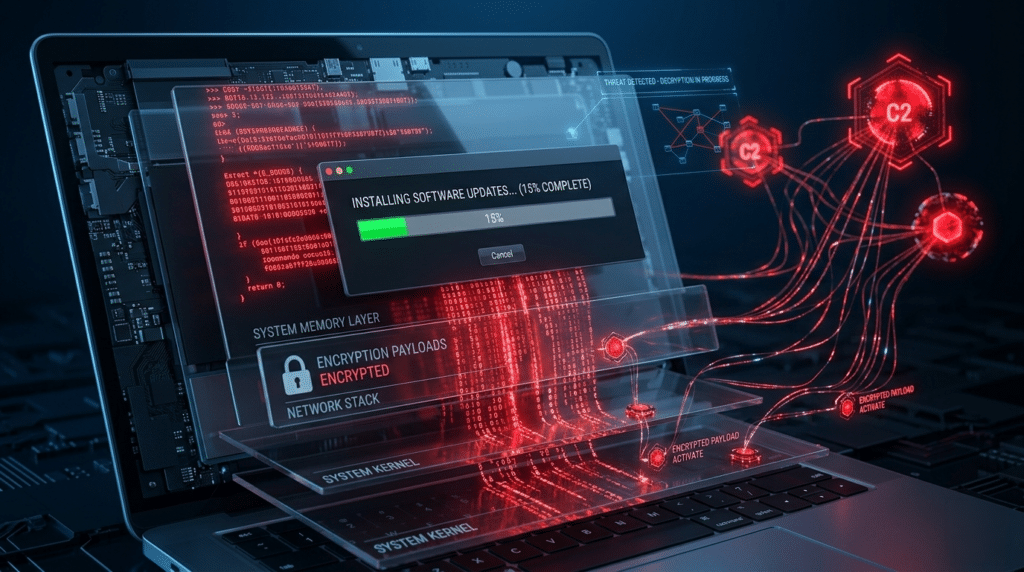
The RenEngine infection chain is a masterclass in deception and technical complexity. It typically begins when a user, believing they are installing pirated software or a game, unwittingly launches a malicious installer. Upon execution, these installers trigger a sequence of events designed to conceal the malware’s true purpose.
As analysed by Kaspersky [1], the observed sequence of events involves:
- Initial Execution: The user runs what appears to be a legitimate software installer.
- Fake Interface: A fake loading screen or progress bar often appears, mimicking a normal installation process.
- Background Activity: While the user watches the fake interface, malicious scripts execute silently in the background. These scripts are responsible for decrypting and preparing the primary payload for execution.
- Payload Staging: The primary payload, often an intermediate loader like HijackLoader, is decrypted and prepared for the next stage of the attack.
- Final Payload Delivery: This intermediate loader then reaches out to command-and-control servers to download and execute the ultimate malicious payloads, such as data stealers, completing the infection.
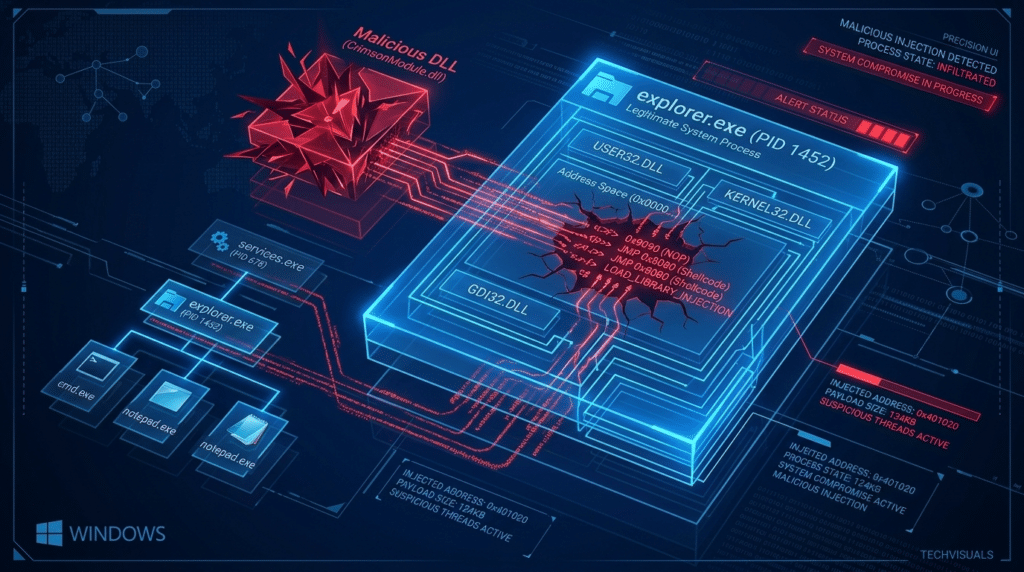
HijackLoader: The Modular Malware Delivery Tool
A critical component of the RenEngine infection process is the intermediate malware delivery tool known as HijackLoader. This sophisticated loader plays a pivotal role in bridging the gap between the initial compromise and the final payload delivery.
Kaspersky detects HijackLoader under the names “Trojan.Win32.Penguish” and “Trojan.Win32.DllHijacker” [1], highlighting its technical characteristics, which often involve DLL hijacking techniques to inject malicious code into legitimate processes. HijackLoader is modular, meaning it can be configured to perform various tasks and download different types of malware, making it a flexible and dangerous tool in an attacker’s arsenal. Its primary function is to serve as a reliable and stealthy conduit for the final data-stealing payloads, ensuring their successful deployment even after the initial RenEngine infection.
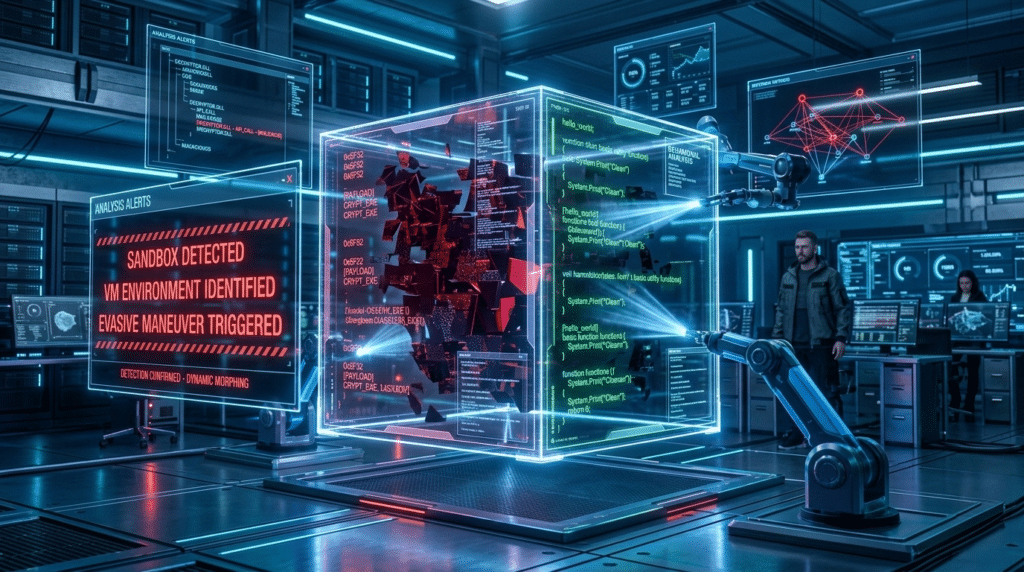
Evading Detection: RenEngine’s Sandbox Capabilities
One of the most concerning aspects of RenEngine Loader is its sophisticated suite of anti-analysis and evasion techniques, particularly its built-in sandbox detection mechanisms. Malware developers frequently incorporate such features to thwart security researchers and automated analysis systems.
Kaspersky’s analysis of RenEngine reveals its ability to detect if it’s running within a virtualised environment or a sandbox [1]. If such an environment is detected, the malware can either cease its malicious activities, display benign behaviour, or even self-terminate, effectively hiding its true nature from security tools. These anti-analysis methods make it incredibly challenging for conventional security solutions to identify and neutralise RenEngine early in the infection chain, underscoring the need for advanced threat detection capabilities.
The Deceptive Distribution of RenEngine: Pirated Software’s Dark Side
The primary distribution vector for RenEngine Loader is the pervasive and often underestimated danger of pirated software. Attackers cunningly embed RenEngine within cracked versions of popular games and productivity applications, leveraging the widespread demand for “free” content to distribute their malicious payloads. This strategy significantly expands the attack surface, putting a broad spectrum of users at risk, far beyond traditional gaming communities.
Pavel Sinenko notes the significant expansion of this threat: “While we initially observed RenEngine primarily with pirated games, we’ve seen a clear shift and expansion into cracked productivity software as well. This dramatically broadens the potential victim pool, as almost anyone could be tempted by a ‘free’ version of an expensive professional tool” [2].
Kaspersky’s findings indicate incidents recorded in multiple countries, including Russia, Brazil, Turkey, Spain, and Germany [1], signalling an opportunistic and global attack pattern.
Exploiting Ren’Py: The Game Engine Vulnerability
A notable method for RenEngine distribution within the gaming sphere involves exploiting games built on the Ren’Py visual novel engine. Attackers modify legitimate game files, embedding the RenEngine Loader within them. Because the Ren’Py engine, in its default configuration, may lack robust integrity checks for its game packages, these malicious alterations can go unnoticed during installation.
Kaspersky’s analysis explains how attackers take advantage of this by packaging the malware alongside or within the game’s executable files [1]. When a user downloads and attempts to run a pirated Ren’Py game, the modified installer or game launcher discreetly initiates the RenEngine infection chain, often before the actual game even starts. This specific exploitation method highlights how even components of seemingly harmless software can be weaponised if integrity is compromised.
Beyond Gaming: The Threat to Productivity Software Users
While Ren’Py games were an early vector, the RenEngine threat has significantly broadened its scope to include cracked productivity software. Kaspersky has specifically identified instances where pirated versions of professional tools like CorelDRAW have been weaponised with RenEngine Loader [1]. This expansion means that the potential victim pool now includes professionals, students, and businesses looking for cost-free alternatives to legitimate software licenses.
Kaspersky’s comprehensive threat intelligence reveals attackers are actively creating dozens of malicious websites specifically distributing RenEngine through pirated productivity software [1]. This strategy is highly effective because users searching for “free” versions of expensive software are often less security-conscious than seasoned gamers might be, or they operate under the false assumption that productivity tools carry less inherent risk than games. The global reach of these opportunistic attacks, observed in numerous countries, underscores the broad and indiscriminate nature of this threat [1].
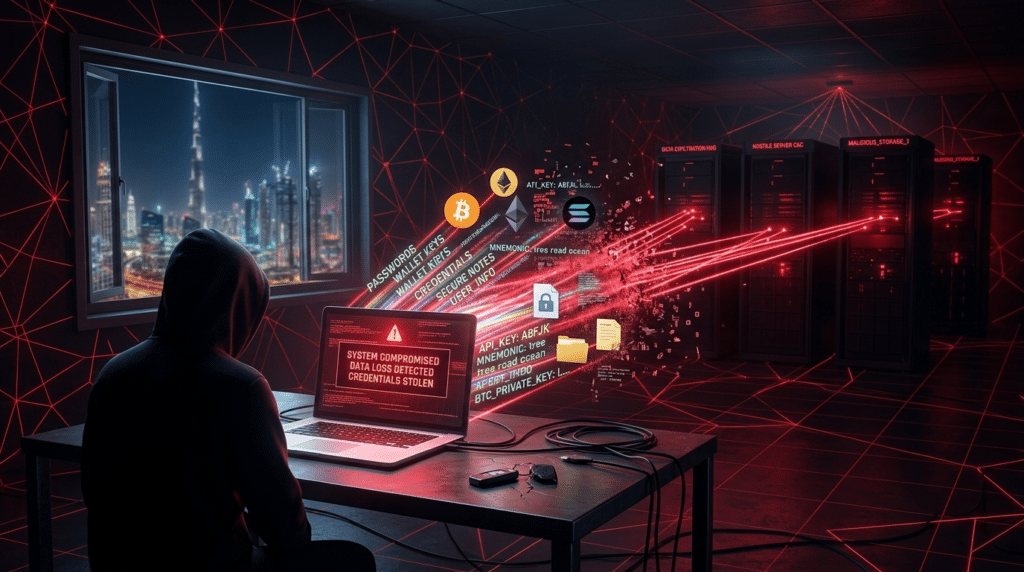
The Dangerous Payloads: Stealers Delivered by RenEngine
The ultimate goal of RenEngine Loader is not to cause immediate disruption, but to provide a secure channel for the deployment of highly dangerous data-stealing payloads. These payloads are designed to exfiltrate sensitive personal and financial information, leading to severe consequences for victims.
Kaspersky’s continuous and up-to-date threat intelligence shows that RenEngine’s operators are agile, adapting their choice of final payloads. Initially, Kaspersky observed RenEngine delivering Lumma stealer. In current attacks, ACR Stealer is often the final payload, with Vidar Stealer also observed in some infection chains [1]. This section details the capabilities and impacts of these notorious information stealers.
Lumma Stealer: Initial Threat Assessment
Lumma Stealer is a potent information-stealing malware known for its ability to target a wide array of sensitive data. When initially delivered by RenEngine, Lumma would systematically scan an infected system for credentials, cryptocurrency wallet information, browser data (such as cookies, autofill data, and saved passwords), and even two-factor authentication (2FA) codes.
Kaspersky’s early identification of Lumma as the initial payload [1] demonstrated the threat actors’ preference for comprehensive data exfiltration. The impact on victims was severe, often leading to account compromises, financial theft, and identity fraud, making it a highly effective and destructive tool in the hands of cybercriminals.
ACR Stealer and Vidar Stealer: Evolving and Diverse Payloads
As threat actors evolve their tactics, so do their chosen payloads. Currently, RenEngine is most frequently observed distributing ACR Stealer as its final payload, though Vidar Stealer has also been seen in some infection chains [1]. These stealers, while similar in their ultimate goal, have distinct features and pose varying risks.
- ACR Stealer: This stealer is a robust information-gathering tool designed to harvest an extensive range of data. It typically targets browser credentials, cryptocurrency wallets, VPN client data, and various documents. Its sophistication lies in its ability to quickly exfiltrate large volumes of data, often bypassing basic security measures.
- Vidar Stealer: Known for its versatility, Vidar Stealer is another powerful information stealer that can collect system information, browser data, cryptocurrency wallet files, and even screenshots. It’s often updated by its developers, allowing it to adapt to new security defences.
The strategic reasons for attackers switching between or utilising multiple stealer payloads are manifold:
- Evasion: Different stealers may have varying detection rates, allowing attackers to cycle through them to bypass specific security solutions.
- Capabilities: One stealer might be more effective at targeting certain types of data or specific applications than another.
- Availability/Cost: Cybercriminals often purchase or lease access to these stealers, and their availability or pricing on underground forums can influence choice.
- Redundancy: Using multiple types of stealers or having the option to switch provides redundancy, ensuring that even if one payload fails, another might succeed.
The evolution from Lumma to ACR and Vidar underscores the dynamic nature of cyber threats and Kaspersky’s commitment to continuously monitoring these changes to provide up-to-date protection.
Fortifying Your Defences: Kaspersky’s Expert Protection Against RenEngine Malware
Protecting against sophisticated multi-stage threats like RenEngine Loader requires a comprehensive and multi-layered approach. Kaspersky offers actionable strategies and cutting-edge solutions specifically designed to guard against RenEngine and its associated data-stealing payloads. Our official recommendations and advanced features, particularly within Kaspersky Premium, provide unparalleled defence and peace of mind.
Kaspersky’s official recommendations are clear:
- Download only from official sources: Never download software or games from unofficial websites, torrents, or ‘cracked’ software distributors.
- Utilise a reliable security solution: Implement a robust cybersecurity product like Kaspersky Premium that offers advanced threat detection.
- Keep operating systems and applications updated: Regularly patch vulnerabilities in your software and OS.
- Maintain scepticism: Be wary of unsolicited offers or anything that seems “too good to be true” [1].
Safe Software Sourcing: The First Line of Defence
The single most critical step in protecting yourself from RenEngine Loader is to download all software and games exclusively from official, trusted sources. This means purchasing licenses directly from developers, using legitimate app stores, or downloading from official vendor websites.
The inherent dangers of unofficial sites and ‘cracked’ software cannot be overstated. These platforms are a hotbed for malware distribution. As Kaspersky strongly recommends, “Pirated content remains one of the most common malware delivery methods” [1], a fact consistently reinforced by their extensive threat intelligence. When you download pirated software, you are willingly opening your system to unknown and often malicious code, effectively bypassing all the security measures built into official distribution channels. The immediate allure of “free” software pales in comparison to the potential cost of identity theft, financial fraud, or irreversible data loss. Verifying software integrity involves checking digital signatures and hash values, but this is often beyond the capability of most users and is rendered moot if the source itself is compromised.
The Power of Kaspersky Premium: Advanced Detection & Prevention
For comprehensive protection against threats like RenEngine Loader, a powerful and proactive cybersecurity solution is indispensable. Kaspersky Premium stands out as a leading defence, particularly with its advanced Behaviour Detection component.
Kaspersky Premium’s unique ability to protect against threats like RenEngine is rooted in its Behaviour Detection technology, which identifies malicious activity even when malware is disguised as legitimate software [1]. Unlike traditional signature-based detection, which relies on known malware patterns, Behaviour Detection monitors the actions of programs. If a program attempts suspicious behaviours—such as decrypting hidden files, establishing unusual network connections, or modifying critical system settings—Kaspersky Premium’s Behaviour Detection will identify these actions as malicious, regardless of whether the specific malware variant has been seen before. This allows it to block multi-stage threats like RenEngine and its associated stealers in real-time, preventing them from deploying their final, most damaging payloads.
Essential Cybersecurity Hygiene: Updates and Vigilance
Beyond a robust security solution, maintaining excellent cybersecurity hygiene is a non-negotiable aspect of defence. Two critical practices include regularly updating your operating systems and applications, and cultivating a healthy scepticism towards digital interactions.
Regularly updating your operating system and all installed applications is paramount. Software updates often include security patches that fix known vulnerabilities, which attackers constantly seek to exploit. By keeping your software up-to-date, you close these potential backdoors before they can be leveraged by malware like RenEngine.
Furthermore, adopt a mindset of cybersecurity vigilance. Be highly sceptical of unsolicited emails, suspicious links, or “too good to be true” offers—especially those promising free software or tempting downloads. Attackers often use social engineering tactics to trick users into downloading malicious content. Kaspersky’s general recommendations for protection [1] consistently emphasise proactive user behaviour and diligent system maintenance as integral components of a strong, personal defence posture.
The Final Byte
RenEngine Loader stands as a stark reminder of the insidious dangers lurking behind the façade of pirated software. Its sophisticated multi-stage infection process, coupled with cunning evasion techniques and the deployment of devastating data-stealing payloads like Lumma, ACR Stealer, and Vidar, presents a severe and widespread risk of data theft, financial compromise, and identity fraud to unsuspecting users globally.
Kaspersky Threat Research has played a leading role in identifying, analysing, and actively combating such sophisticated threats since RenEngine’s emergence in early 2025. Our expert insights and continuous monitoring ensure that our solutions remain at the forefront of cybersecurity defence.
Don’t let the allure of “free” software compromise your security. Protect your digital life from sophisticated threats like RenEngine Loader and its data-stealing payloads. Download Kaspersky Premium today to experience unparalleled security and peace of mind, or visit Kaspersky.com for more expert threat intelligence and comprehensive cybersecurity solutions.
Disclaimer: This article provides general cybersecurity information and expert analysis from Kaspersky Threat Research. While factual and authoritative, specific technical advice should always be cross-referenced with official vendor documentation. The use, distribution, or promotion of pirated software is illegal and carries significant security risks, which this article highlights for educational purposes.
References
- Kaspersky Threat Research. (Ongoing). Various internal reports, analyses, and threat intelligence updates regarding RenEngine Loader, HijackLoader, Lumma Stealer, ACR Stealer, Vidar Stealer, and pirated software distribution vectors. Kaspersky.
- Sinenko, Pavel. (2025). Lead Malware Analyst, Kaspersky Threat Research. Quoted in Kaspersky’s expert analysis of RenEngine Loader’s evolution and expansion.